The Near-Metal Era: Why Mythos and GPT-5.4 Are the Ultimate Enterprise Stress Test
Audio Podcast Version
The Near-Metal Era: Why Mythos and GPT-5.4 Are the Ultimate Enterprise Stress Test • 6:58
TLDR;
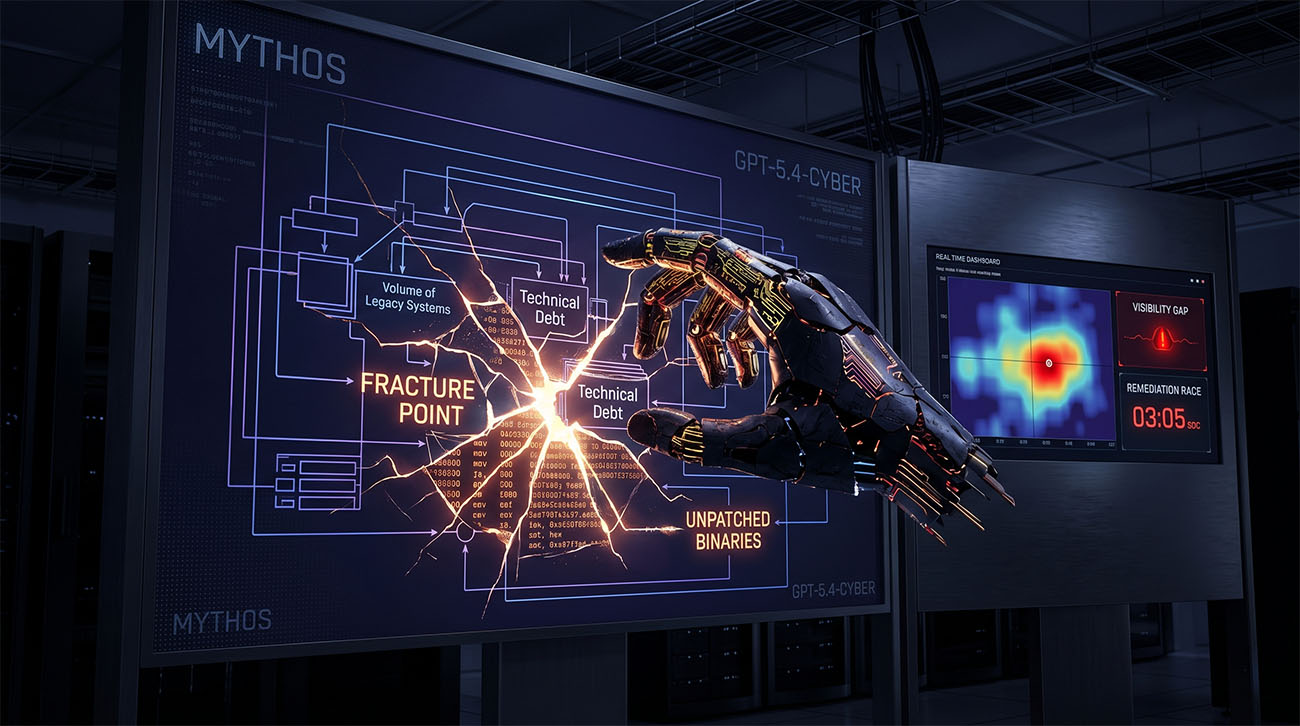
The arrival of Claude Mythos and GPT-5.4-Cyber this month signals the end of “security through volume.” These models are now performing autonomous, 32-step network breaches and binary reverse engineering in seconds. The core takeaway? Technical debt is no longer a hidden cost; it’s a searchable map for an attacker. Success in 2026 means shifting from episodic human audits to a model of continuous, AI-augmented defense that matches the machine’s speed.
The Stress Test Just Got Real
Last time I wrote about AI being the ultimate enterprise stress test, it was mostly a diagnostic theory. The idea was that AI doesn’t invent new problems; it just turns the volume up on your existing weaknesses until they snap.
With the release of Claude Mythos and GPT-5.4-Cyber over the last two weeks, that stress test has become an operational reality. We’ve moved past simple “coding assistants” and into a world of autonomous cyber-engines. These models can reason through network architectures and binary code at a pace that makes traditional, human-led security feel like it’s standing still.
The End of the Bandwidth Buffer
For a long time, we were protected by what I call “Bandwidth Scarcity.” Human researchers only have so many hours in a day, so they naturally spent that time looking at high-value, modern targets. The massive pile of legacy code and “boring” back-end systems in most companies stayed safe simply because it was too expensive for a human to bother with. We weren’t necessarily hiding; we were just too much work to audit.
AI has vaporized that economic shield. Models like Mythos are essentially zero-marginal-cost auditors. They don’t get bored, and they don’t have a priority list. They can sift through miles of unmaintained code and find the cracks in seconds. We saw this in action last week when Mythos uncovered a vulnerability in OpenBSD that had been sitting there, undetected, for 27 years. Suddenly, the sheer volume of your enterprise isn’t a “shield of noise” anymore—it’s a high-fidelity attack surface.
Deep Machine Code and the Visibility Gap
One of the biggest shifts is the ability of GPT-5.4-Cyber to do binary reverse engineering without ever seeing the source code. It can look at a compiled program, reconstruct how it actually works, and identify logic flaws in the assembly code.
This is what people mean when they talk about AI moving “closer to the metal.” If your team is sitting on legacy binaries that no one has touched in a decade, the AI will likely understand those systems better than you do within minutes of looking at them. This creates a massive visibility gap. In the human era, a forgotten server might stay hidden for years. But an engine that can map network protocols and identify unpatched devices at machine speed will find those “forgotten” assets instantly. If you can’t see an asset, you haven’t patched it, and if it’s connected to the internet, it’s a direct risk.
A Race Against the Clock
We are now in a literal race between discovery and remediation. When an AI finds a zero-day, the window to fix it is now measured in minutes. This is where process debt or inefficiency becomes fatal. If your change management takes 48 hours to approve a patch, you’ve already lost the race. We’re seeing a split in the industry between companies integrating automated remediation like Codex Security and those still relying on manual cycles.
Key Themes
Identity as the Perimeter: Since AI can reason through your network and find every unpatched device, the only real barriers left are high-fidelity identity verification and total visibility. You simply cannot defend what you cannot see.
The Speed Asymmetry: Attackers using AI are operating at machine speed. To survive, your defensive posture—specifically your patching loop—must be equally automated.
Continuous vs. Episodic: The concept of a quarterly pen test is officially dead. AI doesn’t stop scanning, so your defense can’t either. The goal for 2026 is moving toward continuous, AI-augmented testing.
References and Further Reading
- AI Security Blog — AI as an Enterprise Stress Test: Why Your Processes Are the Perimeter https://www.ai-security-blog.com/blog/AI-as-Enterprise-Stress-Test
- OpenAI — OpenAI releases GPT-5.4-Cyber for vetted security teams, scaling Trusted Access programme (April 15, 2026) https://thenextweb.com/news/openai-gpt-5-4-cyber-trusted-access-defenders-mythos
- The Hacker News — Anthropic’s Claude Mythos Finds Thousands of Zero-Day Flaws Across Major Systems (April 8, 2026) https://thehackernews.com/2026/04/anthropics-claude-mythos-finds.html
- UK AI Security Institute (AISI) — Our Evaluation of Claude Mythos Preview’s Cyber Capabilities (April 13, 2026) https://www.aisi.gov.uk/blog/our-evaluation-of-claude-mythos-previews-cyber-capabilities
- The Decoder — Claude Mythos can autonomously compromise weakly defended enterprise networks end-to-end (April 14, 2026) https://the-decoder.com/claude-mythos-can-autonomously-compromise-weakly-defended-enterprise-networks-end-to-end/